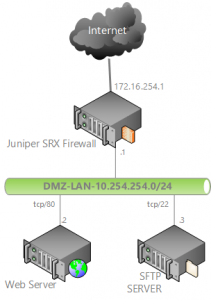
Resumo: Redirecionamento de portas usando CLI no Juniper SRX 240
SO: JUNOS Software Release [10.0R3.10]
1 – Configurar as entradas dos endereços das entidades:
set security zones security-zone DMZ-trust address-book address WebServer 10.254.254.2/32 set security zones security-zone DMZ-trust address-book address SftpServer 10.254.254.3/32
2 – Tradução das configurações de portas (nome para número):
set applications application HTTP protocol tcp set applications application HTTP destination-port 80 set applications application SSH protocol tcp set applications application SSH destination-port 22
3 – CONFIGURAÇÕES DE NAT
Ambos servidores e portas definidos com seus ips privados:
set security nat destination pool dnat_10_254_254_2m32 address 10.254.254.2/32 port 80 set security nat destination pool dnat_10_254_254_3m32 address 10.254.254.3/32 port 22
4 – Politica de Nat que faz a tradução:
set security nat destination rule-set DEST-NAT from zone untrust
Para o Web Server:
set security nat destination rule-set DEST-NAT rule WEB-SERVER-TCP-80 match destination-address 172.16.254.1/32 set security nat destination rule-set DEST-NAT rule WEB-SERVER-TCP-80 match destination-port 80 set security nat destination rule-set DEST-NAT rule WEB-SERVER-TCP-80 then destination-nat pool dnat_10_254_254_2m32
Para o SFTP
set security nat destination rule-set DEST-NAT rule SFTP-SERVER-TCP-22 match destination-address 172.16.254.1/32 set security nat destination rule-set DEST-NAT rule SFTP-SERVER-TCP-22 match destination-port 22 set security nat destination rule-set DEST-NAT rule SFTP-SERVER-TCP-22 then destination-nat pool dnat_10_254_254_3m32
5 – Configuração de Política de Segurança, IPs privados e portas de servidor Web e SFTP Server são definidos aqui:
para o Web Server:
set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match source-address any set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match destination-address WebServer set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match application HTTP set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ then permit
para o SFTP Server
set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match source-address any set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match destination-address SftpServer set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ match application SSH set security policies from-zone untrust to-zone DMZ-trust policy INTERNET-TO-DMZ then permit